John Walker | July 18th, 2016
In the world of industrial control systems, “Remote Access” means different things to different people. It can be as simple as seeing historical data remotely to taking full control of a system from the opposite side of the world. There are many ways that you can remotely connect to a system, some that are secure and some that are not so secure.
Before we go into some options, there are a couple of ways that you could look at this question. Do you need to access the control system outside of the plant or strictly within the plant itself?
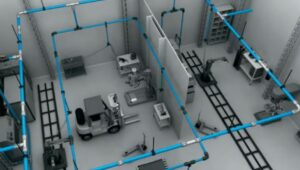
Internal Plant Remote Access
For inside the plant only, you can use Remote Desktop Protocol (RDP), which is built into Windows operating systems.
With Remote Desktop, you can set up a tablet to access graphics and control the system from outside of the control room. You can also consider using a wireless access point and a tablet to provide remote control in the field. This is fairly simple to set up and provides operations, engineering, and maintenance the ability to work on equipment in the field, while looking at the system live on a tablet. Just be sure to adhere to area classifications if using this method.
External Plant Remote Access
For remote access outside your plant, common options include cell modems, security switches, VPN, or a cloud based VPN.
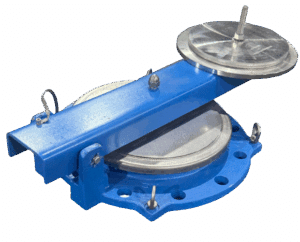
The simplest method is to connect the computer to a LAN or WAN and remotely access it with freeware, which is readily available for download from the internet. This is not common in industrial applications due to security concerns, but it is easily done. In lieu of that, you might want to look at other, more robust, options. There are a number of security switches on the market which act as a hardware firewall for a VPN and or with a Cell Modem.
VPN for Remote Access
Typically, if you want remote access outside the plant, you may need to work through your IT group. If this is the case, you may have some convincing to do. (e.g. Why do you need it?, Do you really need it?, Can you live without it?) These are all reasonable questions and you need to be prepared to answer these and justify the need versus the risk.
If you get past these questions, many companies will require you to use the corporate “approved” VPN. This provides an additional layer of protection, but at the same time it adds significant complexity to the setup connection. If you are using a security switch with your corporate VPN, my one recommendation is that you use one of the approved VPN packages that the switch manufacturer lists. If you choose not to use a recommended or “vendor approved” solution, you can struggle for months trying to get something that has not been tested and approved to work for your application.
Cellular Modems for Remote Access
There are some common concerns about about using cellular to remotely access your control system such as “That’s going to be slower than dial-up” or “Data over a cellular modem will cost me a fortune”. Both of these arguments, while rooted in truth, are a bit outdated and shouldn’t cause you any heartburn.
Cellular Modems are a common alternative these days as the technology and speeds have greatly improved.
New 4G cellular modems allow remote access in real time without any noticeable lag. The 4G cellular modems will also downgrade to 3G if a 4G signal is unavailable. The costs for data service have decreased dramatically over the past few years, allowing for low usage plans of less than $10 per month and higher usage plans for under $20 per month. Doing a site survey to determine the available signal strength at a potential site is also easily done now. It is no more complex than carrying in a 4G phone and checking the signal strength.
The cellular modem is not set up to require you to dial into it, rather it is provided with a static IP address which can be pinged remotely. This may seem like a hacking risk and, while that is true, there are several things that you can do to reduce that threat. Many carriers now offer the customer virtual “VPN” cellular networks so that the IP address is not easily identified out on the internet.
I would recommend using an additional protection layer such as a hardware firewall between the cellular modem and the control system. The firewall will additional protection such a MAC address identification and the requirement for a specific username and password to prevent unauthorized access.
I have a customer who recently installed a cellular modem with a security switch, and they are able to have an engineer troubleshoot their DCS in real time from a remote location. The way they insure unauthorized access is that they never connect the modem to the security switch until they need remote assistance. When they call the remote engineer, they simply connect the cellular modem to the switch and, once he provides the authentication, he can access the engineering station. This is a minor inconvenience, but it prevents the system from staying online and exposed to outside threats and gives the plant total control over when access to their system is allowed. We have also designed panels to allow an operator to set a timer to allow access and when the timer goes it access is cut off. This is just in case the operator forgets to unplug the network cable.
Even without a security switch, there are several security options natively available in cell modems. The cell modems that we use have VPN Tunneling, Access Control Lists, IP Address Lockdown, and out of the box 1024 bit encryption. For comparison, your online banking probably uses 128 or 256 bit encryption. In order to get through the modem to your system, a hacker would have to log in through the web GUI, hack the username and password, activate the firewall tunnel, and then activate the VPN Tunnel, before gaining access to your network.
Alternative Remote Access Options
There are also many different remotely hosted or cloud based remote access solutions from various vendors including Cisco VPN, Siemens, Rockwell, Phoenix mGuard Secure Cloud. The key to these offerings is that the initiation for the connection always emerges from within your system before the actual connection is made. This is similar to the process used when getting tech support from Microsoft or other software vendors.
If you are looking for a way to either access data remotely, or are trying to monitor or engineer your process remotely, there are many options available on the market. From very cost effective methods to more expensive hosted solutions I encourage you to first look at what level of interaction versus your security levels needed, and then fully research your options or call in your local integrator to help.