Robbie Peoples, P.E. | June 19th, 2015
For the majority of their existence, industrial control systems (ICS) have been isolated from external access. But with the increased prevalence of computers and the internet in modern society, these once isolated systems are being exposed to the world.
This exposure has created a myriad of new security concerns that were impossible to predict when many of these systems were first installed, and because of the mutability of the internet and modern technology, many of these systems are no longer secure against unauthorized access.
One important concept to remember about security in general, is that given unlimited resources and time, an attacker will ALWAYS gain access to a guarded system. Therefore, the main goal of security systems is not to prevent unauthorized access, but to make it as difficult as reasonably possible for an attacker to gain access, without inhibiting normal use.
A good example is the lock on your front door. A lock will prevent someone from just opening the door and walking in, but it won’t prevent someone from breaking it down or simply finding another way. One option to fix this weakness would be to encase the house in cement and post armed guards at the perimeter, but that would likely interfere with your daily activities and be cost prohibitive. The more reasonable solution would be to accept the limitations of your home’s security and to make the most of it by locking the door, not advertising when you’re leaving, etc.
Compared to your house, however, an industrial facility likely has more value to be gained from unauthorized access, and therefore has an increased budget and need for security. The reasonable option is often fences, gates, cameras, and an access control system. These systems won’t stop a determined intruder, but they often provide enough of a deterrent to prevent unauthorized access.
Like your house and an industrial facility, a computer system can only be secured to a reasonable degree, which is usually dictated by a budget and the system’s normal operation. Also like a house and industrial site, a computer system’s security is easiest to bypass by taking advantage of human error.
The common example of this is social engineering, or manipulating someone into divulging protected information, but other examples would be computer viruses or malware accidentally introduced by a user. Unfortunately, this is also one of the hardest security threats to minimize because it requires changing human behavior. Often the better solution is to make it harder for a user to follow unsafe practices. Some simple solutions to this are as follows:
- Require every user to have an individual account and strong password.
- Require passwords be regularly changed.
- If practical, make sure user accounts automatically log off when inactive.
- Use a smart card reader in addition to a username and password.
- Remove CD or floppy drives, and use external USB versions when required.
- Place physical port blockers on all USB ports and connect the keyboard and mouse through PS2 ports.
- Use a virus scanner, if supported, and keep all parts of the system as up-to-date as possible.
- Send out regular reminders to users about not sharing passwords, and other good security practices.
Most of the above practices are relatively inexpensive and will not interfere with normal operation, but will help mitigate many common security weaknesses.
One topic of special note is the idea of a strong password. One of the most common issues with passwords is creating a strong but easy to remember password. The strength of a password is mostly related to its length, and in many cases a longer password is harder to remember. To solve this problem, try using a sentence as a password. A password created like this is far easier to remember, and far harder for a computer to guess, than the typical 8 character password.
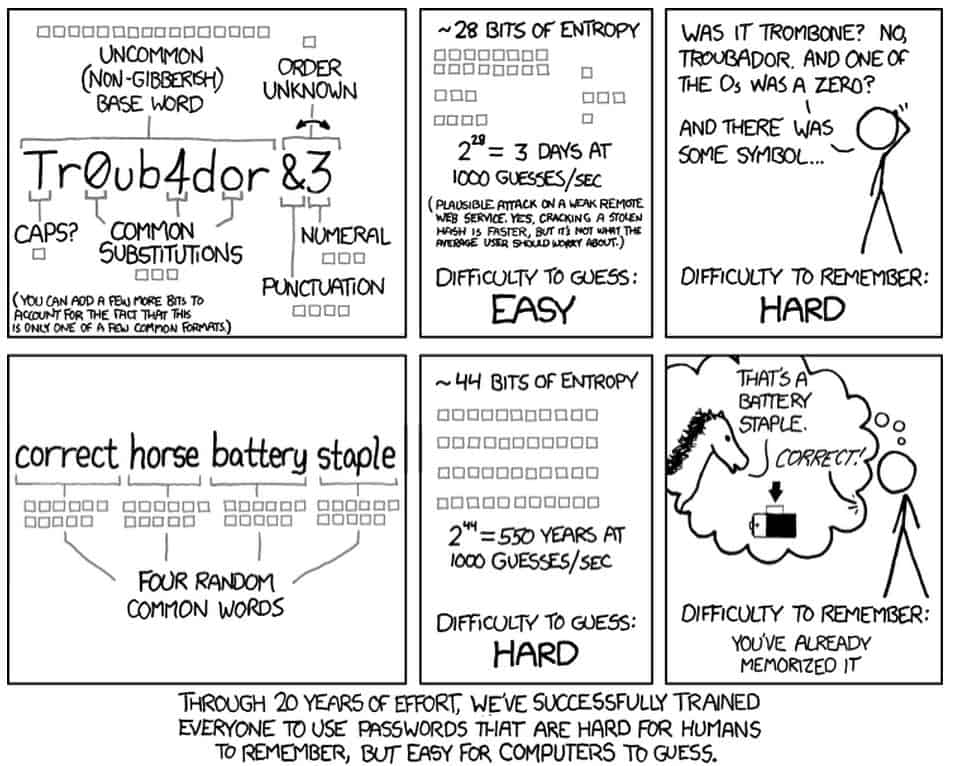
From xkcd.com XKCD Comics are under a creative commons license http://creativecommons.org/licenses/by-nc/2.5/
The next most common method of unauthorized access is poor design with respect to security. Computer and network security is a vast and complicated field, but the basics are simple, easy, and the most important. Because industrial control systems are inherently insecure, the best practice is to keep them completely isolated from any network access. Unfortunately, this is not always possible, so the next best option is to remove any non-essential network access.
This can be done with a properly configured firewall. In this case properly configured means using a whitelist for all inbound and outbound traffic. This is something that needs to be set up by a knowledgeable administrator, and will often be specific to an individual site. It is important to remember that the firewall should be placed at the access point of the ICS, as seen below.
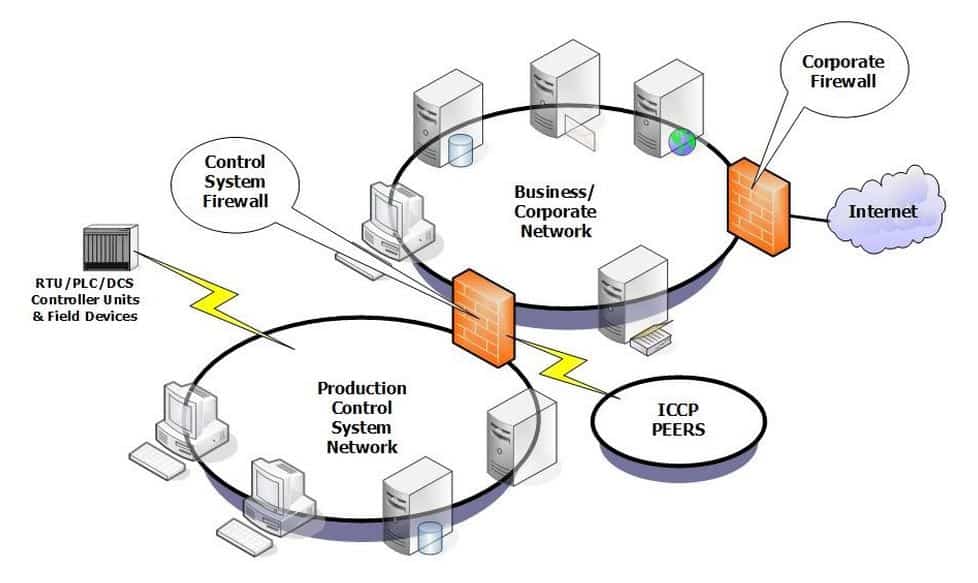
From: Industrial Control Systems Cyber Emergency Response Team
An additional system called an intrusion detection system (IDS) can also be installed and configured. The purpose of an IDS is to alert an administrator to unusual traffic or activity on a network or system. These systems are commonly used in corporate networks, and with proper configuration can add additional security to an ICS. If network access is only needed occasionally, to allow an integrator to work remotely for example (something we highly recommend in our blog, The Benefits of Adding Remote Access to Your DCS System), then a good policy would be to keep the network cable unplugged when not needed.
If wireless access is required ,or the system needs to communicate over the internet, additional security measures will need to be applied. For a wireless network, the best choice is to use WPA2-PSK security with a strong password. Connections over the internet should be passed through a VPN and care should be taken to ensure that any remote connections are on a secure network as well. When setting up a VPN, the best option is to use a certificate instead of a password, as it is often harder to break. Setting up a VPN to use a certificate is trivial in most scenarios for a knowledgeable administrator.
Although the field of computer security and its relation to ICS security is extensive and highly technical, the above recommendations can help mitigate many of the most common and easily exploitable security holes. In the end, the responsibility of security is on the owner of the system, so if security is a major concern to your business then, the best way to ensure there are no weaknesses is to consult an ICS security professional. More information about ICS security, as well as the the latest information on system vulnerabilities, can be found at ics-cert.us-cert.gov.