Eli Jenkins | September 1st, 2017
The following addresses several key points of security threats on the Industrial Control System (ICS). This includes, but is not limited to, all elements of the control layer infrastructure:
- PLC/DCS
- HMI (Eng and Operator Stations) / SCADA / RTU / Web Server
- Instrumentation & Electric Devices
This information should interest the following people:
- Plant Managers
- Engineering Manager
- Operational/Productivity/Reliability Manager or Engineer
- Control System Engineers
- IT/OT Specialists or Engineers
It’s Time to Have a Conversation
Recently, a good friend of mine had a stroke and he was in his very early 40’s. A comment from a family member said that they had not been going to check up appointments or actively thinking about their health. That they were living day-to-day, aware of the risk in the back of their minds, but they had never really had any major problems in the past. They just kept putting it off to later. Now, a life changing event has taken place and there is no going back. They must accept their new reality and move forward as best they can.
It is completely natural to treat these types of things passively (Normalcy Bias), and many get away with it for decades…until they don’t. Some people reading this might not see the comparison from the health of a friend to a cybersecurity article, but the facilities and production plants that make everything we use day-to-day can be subject to drastic “negative change” without anyone that works there being aware.
We treat cybersecurity in our plants much like the way many treat their personal future health. Management and engineers usually realize that there are threats, but capital expenditure requests continue to be denied and delayed due to the fact that those requests are a low priority in the eyes of all involved. Over time, these items become even more passive thoughts and the threats continue to grow right under everyone’s nose.
As a representative for a systems integration company, I work quite often with pharmaceutical and chemical companies. Although most integrators are diligent and careful in their actions, the fact remains that using 3rd party integrators can increase a facility’s security risks more than internal resources. It is rare, in initial project conversations, that any company expresses concern or actively attempts to hold integrators, like my company, accountable by monitoring their work. Although employees really do care about the product, cybersecurity threats are treated with less interest and probability than natural disasters. Then, it strikes. And no one knows where it came from or how long the repercussions will last.
We in the industry have a responsibility to consider any new product or process that might reduce the risk of damage to our system. Not just for our profits or reputation, but for our end customers. My friend had a stroke and his family has to trust the medications and treatments prescribed to him. Whether you think about it or not, the people at the end of your production line are trusting you to consider every possibility and do what you can to prevent threats that can reduce the quality of your product.
“What appears to be an interruption is often an intervention.”
– Rich Wilkerson, Jr.
Threats are growing
If you work in the industry, you have already been pressured to consider some type of security solution. Most solutions that I have seen are quite basic and only partially address the hot topic issues that create easy and quick sales. They are sold as “complete” solutions while they tend to be platform and/or action specific and can often only stop one type of security threat or can interfere with the online operation of your control system.
Be wary of any one stop solution to handle all threats because most of the time it requires a complete action plan. Security in any form takes active engagement by something and/or someone because the nature of the problem is highly variable. The growing rate of technology has an equally growing rate of security threats. Very few security products have advanced enough to create cost effective and efficient solutions. See chart below for the growing threat trend from Kaspersky ICS Systems Vulnerabilities Statistics 2015.
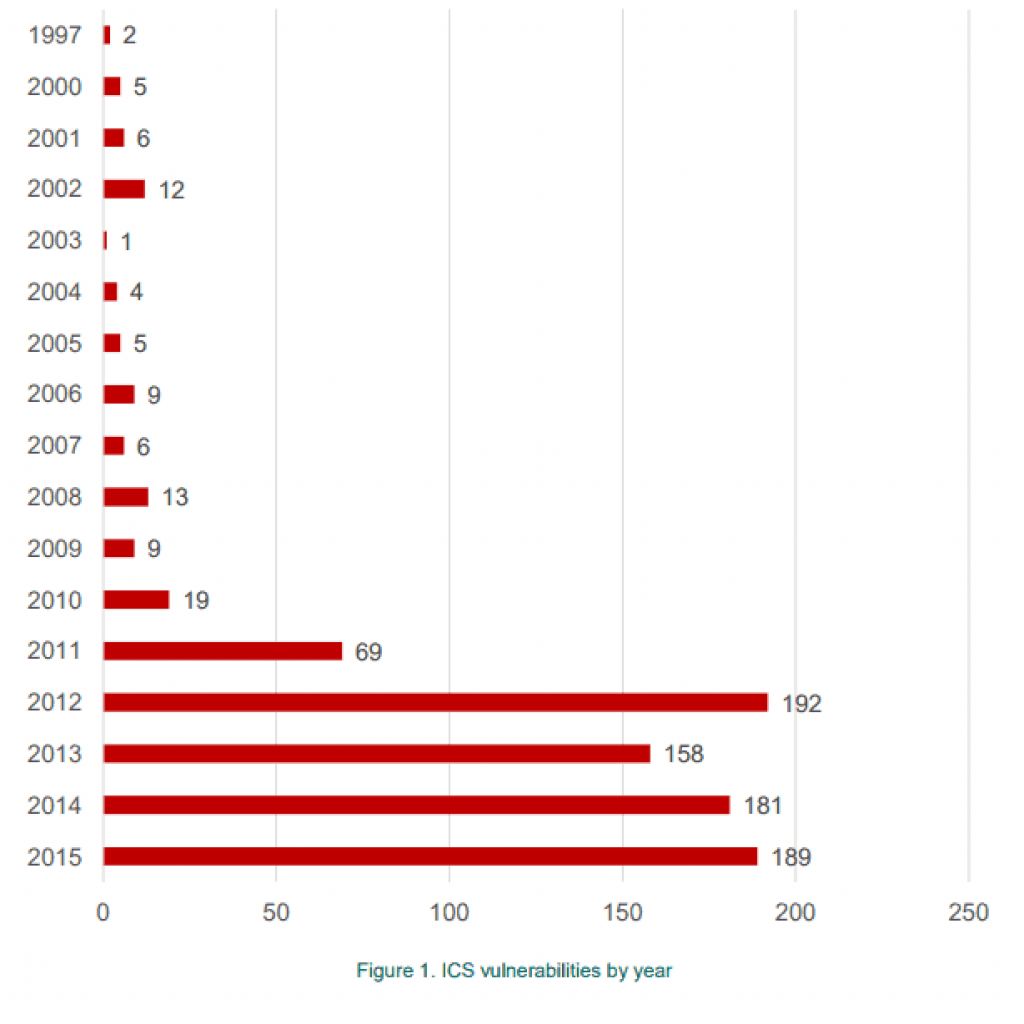
Source: Kaspersky
ICS Vulnerabilities are Widely Diversified
In 2015, new vulnerabilities were found in 55 different manufacturers which included all types of components: PLC/DCS, HMI, electronic devices, SCADA, industrial network devices, and multiple others. The vulnerabilities in ICS components are so different in nature from traditional IT threats that they should be treated differently and with the control engineering team fully participating. Adding firewalls/DMZ, turning off ports, and creating air gaps are good practices, but are not enough and the control layer should always be monitored by equipment/processes designed for the entire control system infrastructure.
Many manufacturers have a solution for this; they sell a product to monitor the control system and help to mitigate the risk. The critical problem I have seen with this method is that they do not have dedicated staff to support the ever growing vulnerabilities and are usually last to the table to mitigate the threat via a patch. These manufacturers also do not play well with other brands. If your facility has multiple types of controllers for example, then you will not get security coverage to some and will have to create multiple solutions that all need to be monitored.
If a process facility relied on conventional security methods – and on security product manufacturers to create patches for security breaches – it would only be partially protected. Firewalls and air gaps are good security precautions but are only part of a complete security solution. See the chart below showing mean time to patch on difference SCADA platforms as an example. Are you comfortable with 125 days to create a patch to mitigate a threat?
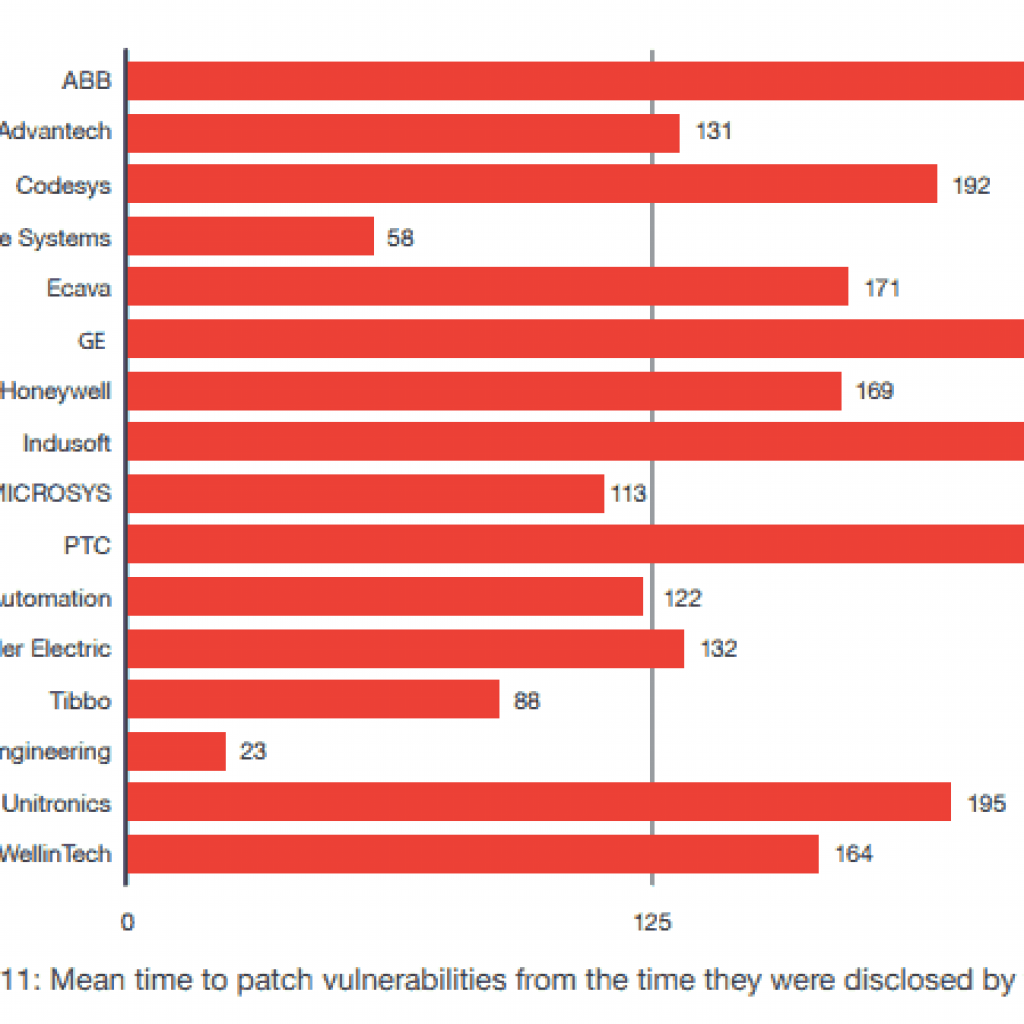
Source: TrendMicro “Hacker Machine Interface“
Most ICS Components are Susceptible
It is probably little shock that the HMI, SCADA, and Controller are the top components that are susceptible to intrusion as these are the main parts of a control system. They are also touched by many different people and systems, all of which bring an element of risk. Whether internal engineers, multiple networks, IT, 3rd party integrators, etc., the risk grows and most companies have no way to track who was on the system and what was done.
I have heard stories from customers about other integrators working on a system, on site or remotely, and updating the firmware on the wrong controller or changing logix in the wrong part of the DCS. Hopefully, the 3rd party integrator doesn’t accidentally pass a security threat to your system because of a sketchy driver download. Unfortunately, most companies would have no way of knowing until the problem surfaces and with a growing number of vulnerabilities, the risk of catastrophic damage is ever increasing.
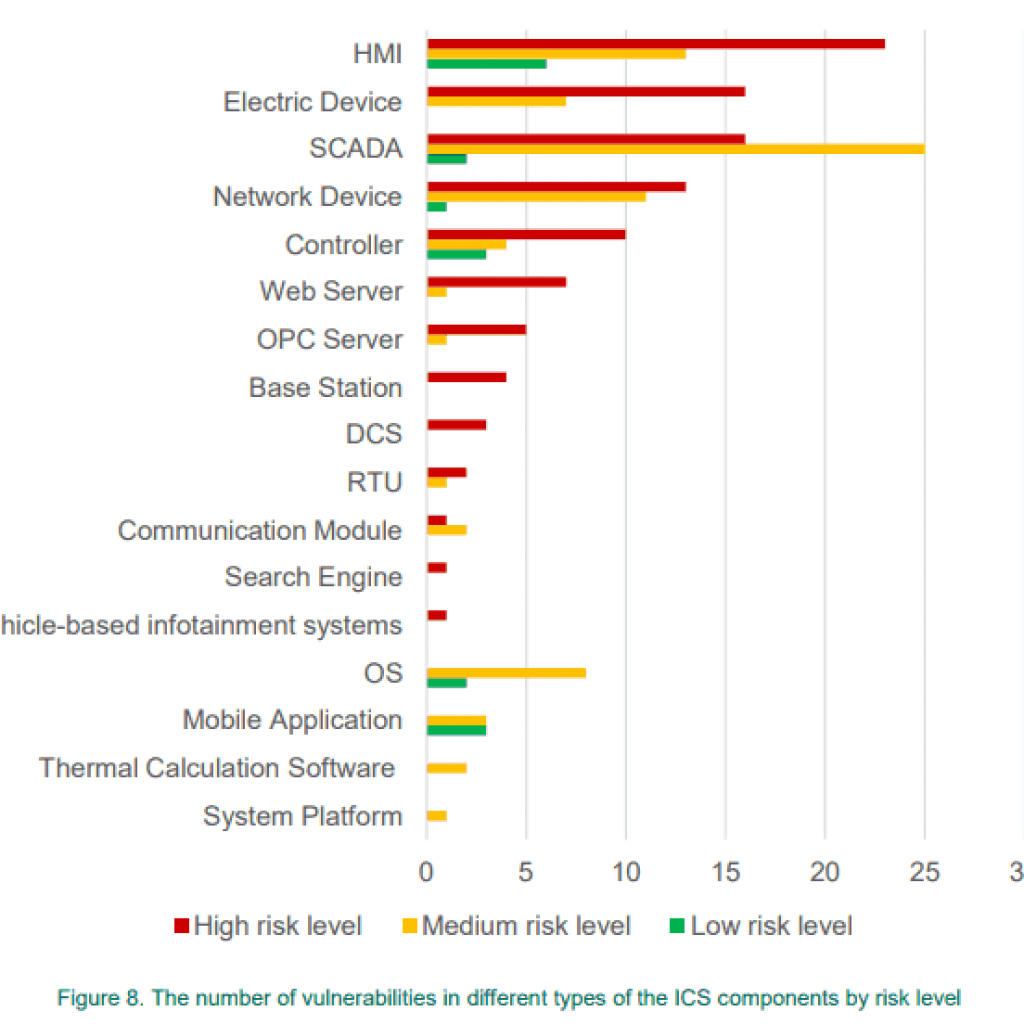
Note: The electric device category consists of distance protection devices, gas detectors, pumps, power analyzers, recloser control, and relay platform units. Source: Kaspersky
Summary
Although automation components are designed for critical infrastructures, industrial-sector devices are not secure by default. The capabilities, motivations, and number of threat actors focusing on ICS environments are increasing. From infected hard drives or USB sticks to unauthorized connections from ICS networks to the Internet through personal smart phones or modems, and from infected distributive kits obtained from vendors, to a hired insider.
With the IIoT growing at an unprecedented rate, these security threats are not going to go away or even slow. Fortunately, this boom has created a movement in the software industry and dozens of startup cybersecurity companies have emerged. Most are trying to make a quick buck on the rising tide; others are inventing technology that our industry has never seen and are taking huge leaps forward in cybersecurity.
When doing your research, look for platform diversity, comprehensive audits, a guarantee of seeing every logic/controller action (audit), real-time alerts, and a qualified, respected team at their foundation. This is uncharted territory and perhaps your usual internal engineer, vendor, or local integrator may not have necessary cybersecurity experience. Reach out to the community. Challenge cybersecurity companies to provide complete solutions, onsite proof of concepts, and a well-respected engineering/security foundation. An option we have found to encompass all of these characteristics is Indegy, which is why we decided to partner with them and provide cybersecurity solutions to our customers. However, no matter what company walks through your door, be sure to deep dive into their solution and ability to support you for the foreseeable future.
Cross Company ISG is currently introducing cutting edge technology in the fields of ICS cybersecurity and IIoT solutions to process manufacturing companies. By implementing an all-inclusive approach to OT safety, our customers reduce costly downtime and successfully mitigate previously unknown or intangible risks.